New Zealand Deploys Spy Agency as Hackers Hit Stock Market
Another day of disruptions in the New Zealand stock market.

(Bloomberg) -- New Zealand called in its spy agency and activated security crisis plans to help defend the stock exchange from overseas attack, after hackers disrupted the market for a fourth straight day.
“We as a government are treating this very seriously,” Finance Minister Grant Robertson said Friday, adding agencies would coordinate to deal with the threat. “There are limits to what I can say today about the action the government is taking behind the scenes due to significant security considerations.”

The NZ$204 billion ($135 billion) stock market has been the target of distributed-denial-of-service attacks that have overwhelmed its website and forced trading halts since Tuesday. The national security plan is typically triggered when a crisis threatens New Zealand’s interests or international reputation.
Authorities haven’t commented on the suspected source of the attacks, which flood a network with Internet traffic and disrupt services, other than saying they originate from offshore. Security intelligence company Akamai warned earlier this week that extortionists claiming to be the Russian-linked hacking group Fancy Bear have recently been sending ransom letters to companies in finance, travel and e-commerce in the Asia Pacific, U.S. and U.K. demanding payments to stop attacks.
New Zealand stock exchange operator NZX is among the companies targeted, the ZDNet website reported, citing an unidentified source in the DDoS mitigation field.
Justice Minister Andrew Little, who oversees the intelligence services, said it would take some time to establish the origin of the attacks. They are more likely the result of criminal activity than being state sponsored, he said.
“We are aware that there have been DDoS attacks in other parts of the world in the finance sector,” he said in an interview, adding the government had consulted with its Five Eyes intelligence partners.
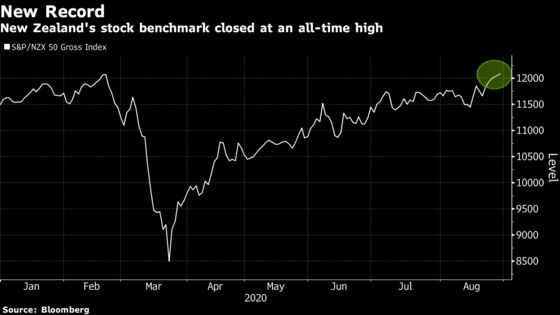
The stock exchange failed to open at 10 a.m. this morning despite assurances from NZX that it would. Trading finally began three hours later at 1 p.m. The market lost an hour of trading on Tuesday, three on Wednesday and almost six hours yesterday from the repeat attacks. Despite the disruption, the market closed at an all-time high Friday.
Little said it was surprising the NZX “appears to have such a vulnerable website and IT architecture.”
“I think now they’ve reflected on that and a plan is now in place for long term remediation,” he said. “My expectation is that they will step up their IT infrastructure and architecture and make sure they are positioned to resist this type of activity in the future.” Steps have been taken to stabilize the website, and work will continue over the weekend, he added.
NZX Chief Executive Officer Mark Peterson said the exchange had been the target of an “ongoing sophisticated and severe” attack and that it was working with Internet provider Spark, government agencies and cyber-security experts in New Zealand and overseas to address the issue.
The disruptions have frustrated investors who were unable to trade amid a busy company earnings season.
‘Hugely Disruptive’
The outages are “hugely disruptive for everyone,” said Michael Midgley, chief executive officer of the New Zealand Shareholders’ Association. “Our main concern, aside from any attempted incursion, is that it is potentially damaging to information flows. In the Covid world the audience is keenly watching to see how reported data relates to forecasts.”

In November, government cyber security agency CERT NZ said it had received reports of extortion emails targeting companies within the financial sector in New Zealand. It said the emails claimed to be from a Russian group called “Fancy Bear/Cozy Bear” and demanded a ransom to avoid denial-of-service attacks. CERT has declined to comment on this week’s attacks.
Fancy Bear is another name for the Russian hacking group APT28, which has been linked to attacks against the U.S. Democratic Party, the White House and NATO. Security experts have also linked it to attacks on European government institutions and private companies and say its primary mission is to gather intelligence in support of the Russian government.
The group sending ransom emails is highly unlikely to be the real Fancy Bear, but is using its name to gain notoriety, according to Yihao Lim, a cyber threat intelligence analyst at Mandiant Threat Intelligence in Singapore.
“It’s plausible that they are cyber gangs calling themselves Fancy Bear involved in this incident,” he said.
©2020 Bloomberg L.P.